“China wants nothing less than to push the US from the Western Pacific and attempt to prevent us from coming to the aid of our allies. But they will fail”
– US Vice President Mike Pence
in his October 4 speech at The Hudson Institute, Washington, D.C
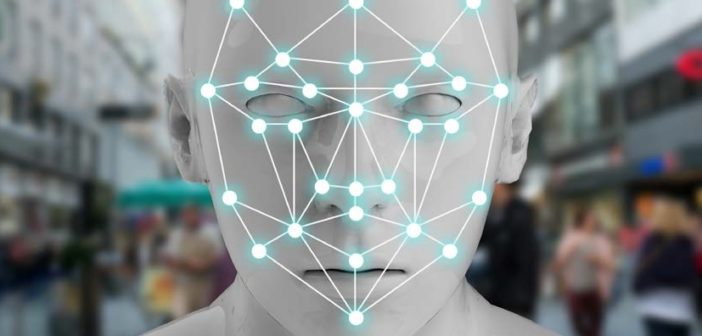
 The security domain remains all encompassing, dictated by the context of the risk or threat. For the Australian security industry, the context should always be viewed internally and externally. Internal factors include, naturally, the needs and direction of the client organisation as well as the domestic threat environment and governance of the industry. However, externally, the macro factors of technological change, globalisation of supply chains and major power geo-politics in our region cannot be ignored.
The security domain remains all encompassing, dictated by the context of the risk or threat. For the Australian security industry, the context should always be viewed internally and externally. Internal factors include, naturally, the needs and direction of the client organisation as well as the domestic threat environment and governance of the industry. However, externally, the macro factors of technological change, globalisation of supply chains and major power geo-politics in our region cannot be ignored.
It would seem security advisors, directors, managers and government legislators need to get to a state of readiness for War. And consider for a moment the implications if we were ever to lose, There is little point in waiting for it to happen before planning and preparing, or worse, assuming it won’t happen. Indeed, in a cyber security context, with the five eye nations now openly attributing cyber attacks against Russia and China, and Australia blocking Chinese technology companies from expanding in the market, the cyber war has already been declared. This is amidst so many other streams of dispute, including the unblinking rises in the ‘trade war’ and to concerning naval manoeuvres between China and US warships in the South China Sea. The West, including Australia, simply does not trust China. And the US is preparing itself for a serious fight.
The 2018 Pentagon Report to Congress on China, stated “China’s military modernization targets capabilities with the potential to degrade core U.S. operational and technological advantages. To support this modernization, China uses a variety of methods to acquire foreign military and dual use technologies, including targeted foreign direct investment, cyber theft, and exploitation of private Chinese nationals’ access to these technologies. Several recent cases and indictments illustrate China’s use of intelligence services, computer intrusions, and other illicit approaches to obtain national security and export-restricted technologies, controlled equipment, and other materials.”…Click here to read full article.